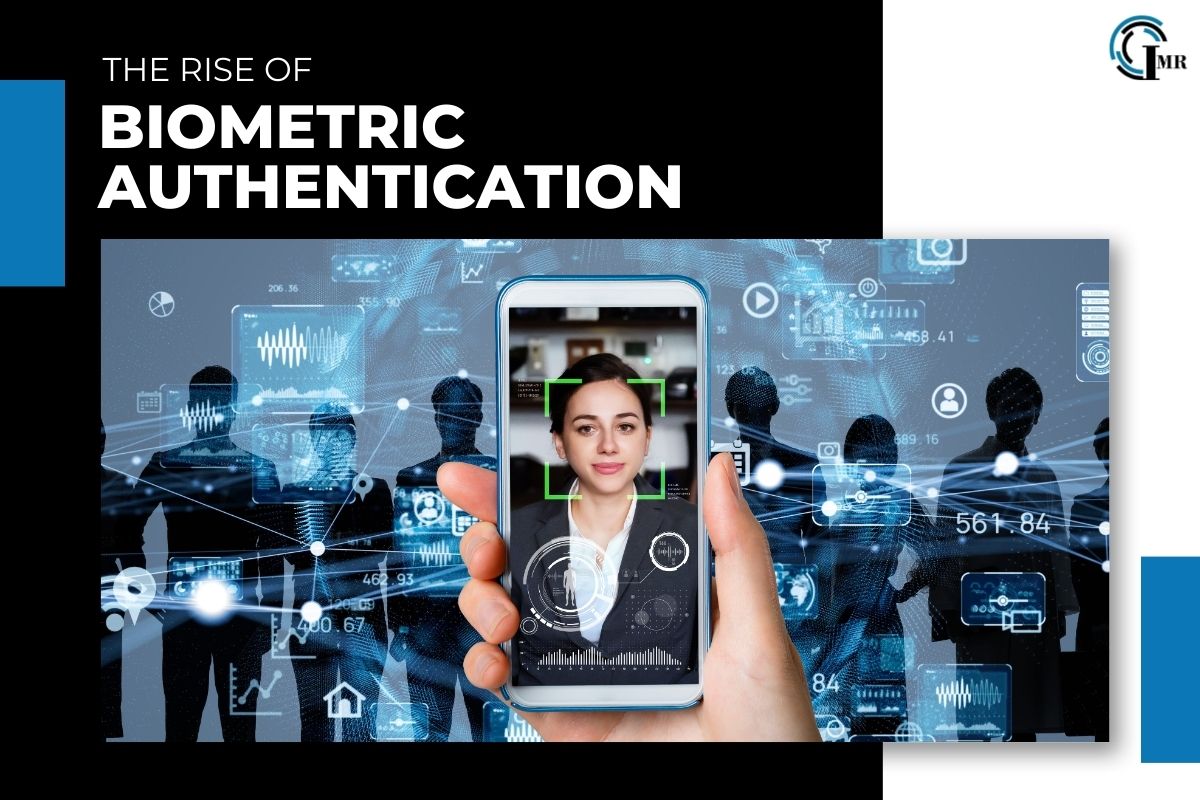
In an era where digital security is paramount, traditional methods of authentication such as passwords and PINs are increasingly being supplemented—or even replaced—by biometric authentication. It leverages unique physical or behavioral characteristics to verify an individual’s identity, offering a more secure, convenient, and reliable means of access control. In this article, we explore the evolution, applications, benefits, and challenges of biometric authentication in today’s digital landscape.
The Evolution of Biometric Authentication:
The concept dates back centuries, with ancient civilizations using physical characteristics such as fingerprints and facial features for identification purposes. However, it wasn’t until the advent of modern computing and advances in biometric technology that authentication became feasible on a large scale. Over the years, biometric verification has evolved from rudimentary fingerprint scanners to sophisticated systems capable of recognizing a wide range of biometric traits, including fingerprints, iris patterns, voiceprints, facial features, and even behavioral patterns such as typing speed and gait.
Applications of Biometric Authentication:

It has found widespread adoption across various industries and applications, including:
Mobile Devices: Many smartphones and tablets now feature identity verification mechanisms such as fingerprint scanners, facial recognition, and iris scanners, allowing users to unlock their devices securely and conveniently.
Access Control: Identity authentication is commonly used to control access to physical spaces such as office buildings, government facilities, and high-security areas. Biometric door locks, fingerprint scanners, and facial recognition systems are deployed to ensure that only authorized individuals can enter.
Financial Services: Banks and financial institutions utilize biometric identification to verify the identity of customers accessing online banking services, authorizing transactions, and withdrawing cash from ATMs.
Healthcare: Biometric verification is employed in healthcare settings to secure electronic health records, control access to sensitive medical information, and prevent unauthorized personnel from accessing restricted areas.
Border Security: Identity Verification is increasingly used at border crossings and airports for identity verification and passenger screening, enhancing security and expediting the travel process.
Benefits of Biometric Authentication:
The adoption offers several benefits over traditional authentication methods, including:
Enhanced Security: Biometric traits are unique to each individual and difficult to replicate, making biometric verification more secure than passwords or PINs, which can be easily forgotten, stolen, or compromised.
Convenience: Identity verification eliminates the need to remember complex passwords or carry physical tokens, streamlining the authentication process and improving user experience.
Accuracy: Identity authentication systems boast high levels of accuracy and reliability, minimizing false positives and false negatives and reducing the risk of unauthorized access.
Scalability: Biometric authentication can scale to accommodate large user populations without sacrificing security or performance, making it suitable for organizations of all sizes.
Compliance: Biometric verification helps organizations comply with regulatory requirements such as the General Data Protection Regulation (GDPR) and the Health Insurance Portability and Accountability Act (HIPAA), which mandate stringent data protection measures and identity verification standards.
Challenges and Considerations:

Despite its many benefits, biometric authentication is not without its challenges and considerations. These include:
Privacy Concerns: Biometric data is highly sensitive and raises concerns about privacy, data protection, and consent. Organizations must implement robust privacy policies and security measures to safeguard biometric information from unauthorized access or misuse.
Biometric Spoofing: Biometric systems are vulnerable to spoofing attacks, where adversaries attempt to bypass security measures by presenting fake or stolen biometric data. To mitigate this risk, organizations must deploy anti-spoofing techniques and biometric liveness detection algorithms.
Interoperability: Biometric verification systems may encounter interoperability issues when integrating with existing IT infrastructure or third-party applications. Standardization efforts and open-source solutions can help improve interoperability and compatibility.
User Acceptance: Some users may be hesitant to adopt identity verification due to concerns about reliability, accuracy, or intrusiveness. Educating users about the benefits and limitations of biometric technology and addressing their concerns can help increase acceptance and adoption rates.
Legal and Ethical Considerations: Identity Verification raises complex legal and ethical issues related to consent, data ownership, and discrimination. Organizations must navigate regulatory requirements and ethical considerations to ensure compliance and uphold user rights and privacy.
Advancements in Biometric Technology:
Recent advancements in biometric technology have expanded the capabilities and applications of biometric verification. These advancements include:
Multimodal Biometrics: Multimodal biometric systems combine multiple biometric modalities, such as fingerprints, facial recognition, and iris scans, to enhance accuracy and security. By utilizing multiple biometric traits, multimodal systems offer greater robustness and resilience against spoofing attacks.
Deep Learning and AI: Deep learning algorithms and artificial intelligence (AI) techniques are increasingly being employed to improve biometric recognition accuracy and performance. These advanced algorithms can analyze complex patterns and features in biometric data, leading to more reliable identification and authentication results.
Continuous Authentication: Continuous authentication solutions continuously monitor users’ biometric traits throughout their interaction with a system or application, providing ongoing verification and enhancing security. This approach minimizes the risk of unauthorized access by detecting anomalies or unauthorized users in real time.
Biometric Fusion: Biometric fusion techniques combine information from multiple biometric sources to enhance authentication accuracy and reliability. By fusing data from different biometric modalities or sensors, such as fingerprint and facial recognition, biometric fusion systems can improve recognition rates and reduce false acceptance and rejection rates.
Passive Biometrics: Passive identity verification methods leverage behavioral biometrics, such as typing dynamics, gait analysis, and voice recognition, to authenticate users without requiring explicit action or interaction. Passive biometrics offer seamless and frictionless authentication experiences while enhancing security and user privacy.
Emerging Trends :

Looking ahead, several emerging trends are shaping the future of biometric authentication:
Wearable Biometrics: Wearable devices equipped with biometric sensors, such as smartwatches and fitness trackers, are becoming increasingly popular for authentication and identity verification. These devices offer convenient and unobtrusive biometric identification options, particularly in scenarios where traditional authentication methods are impractical or inconvenient.
Behavioral Biometrics: Behavioral biometrics, which analyze patterns of user behavior, are gaining traction as a complementary authentication method to traditional biometric modalities. Behavioral biometrics can detect subtle cues and anomalies in user behavior, such as typing speed, mouse movements, and touchscreen interactions, to authenticate users with high accuracy.
Biometric Cryptography: Biometric cryptography combines biometric verification with cryptographic techniques to enhance security and privacy in digital transactions and communications. By integrating biometric data into cryptographic protocols, biometric cryptography ensures secure and tamper-proof authentication and key exchange processes.
Zero-Trust Security: Zero-trust security models, which assume that every user and device accessing a network is untrusted until proven otherwise, are driving the adoption of biometric authentication as part of a comprehensive security strategy. It plays a critical role in verifying the identity of users and devices and granting access to resources based on contextual factors and risk assessments.
Decentralized Biometrics: Decentralized biometric identification solutions, which store and process biometric data locally on user devices rather than central servers, are gaining popularity due to their privacy-enhancing features and resistance to centralized data breaches. Decentralized biometrics give users greater control over their biometric data and reduce the risk of unauthorized access or misuse.
Conclusion:
In conclusion, biometric authentication represents a significant advancement in digital security, offering unparalleled levels of security, convenience, and reliability. From mobile devices and access control systems to financial services and healthcare, identity verfication is revolutionizing the way we verify identity and secure sensitive information. However, as biometric technology continues to evolve and proliferate, organizations must address privacy concerns, mitigate security risks, and navigate legal and ethical considerations to ensure responsible and ethical deployment of biometric authentication solutions in today’s digital world.